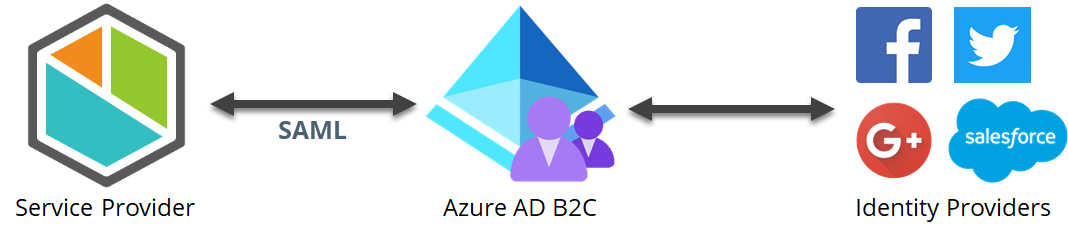
SAML2 Configuration with Azure AD B2C
Overview
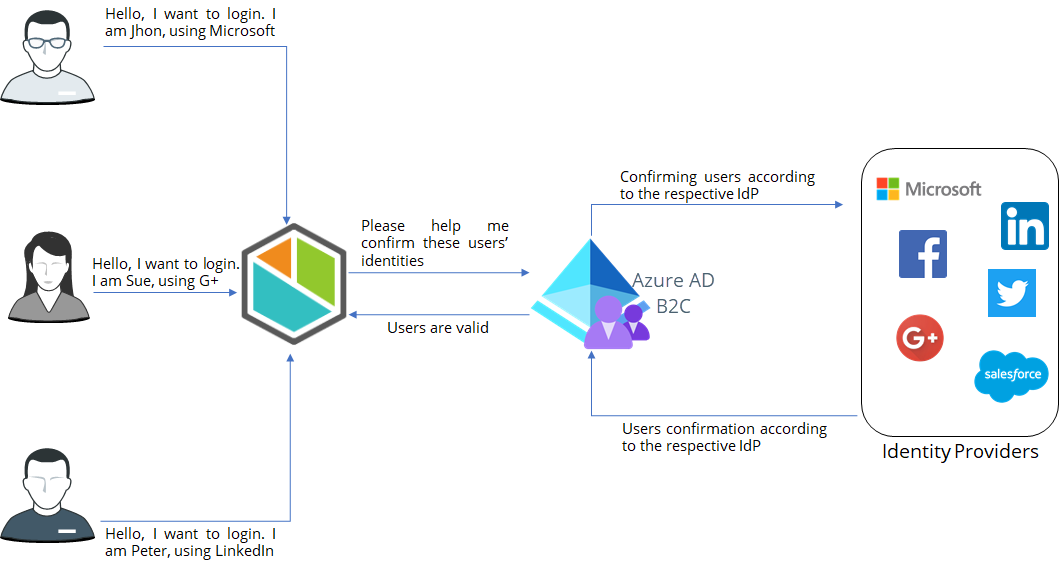
Azure AD B2C is an Identity Access Management system that enables users to use social, enterprise or personal accounts to get SSO access to the application where is configured.
This article provides a step-by-step guide about the configuration needed, both in Azure AD and in Bizagi, to integrate your authentication in Bizagi through Azure AD B2C. Note that these steps are done only once, typically by an admin user of your Customer Portal having access to your Azure AD B2C.
Once you have carried out these steps users sign in to any cloud-based service directly via your Azure AD, as described at Signing in the Bizagi Cloud Portals and Applications.
Before You Start
To configure Azure AD B2C supporting SAML 2.0, you need:
- Have a resource with an Active Directory B2C.
- Create a B2C Tenant inside the Azure AD B2C.
Associate the SAML 2.0 protocol with the B2C
Configure the necessary policies to support SAML 2.0
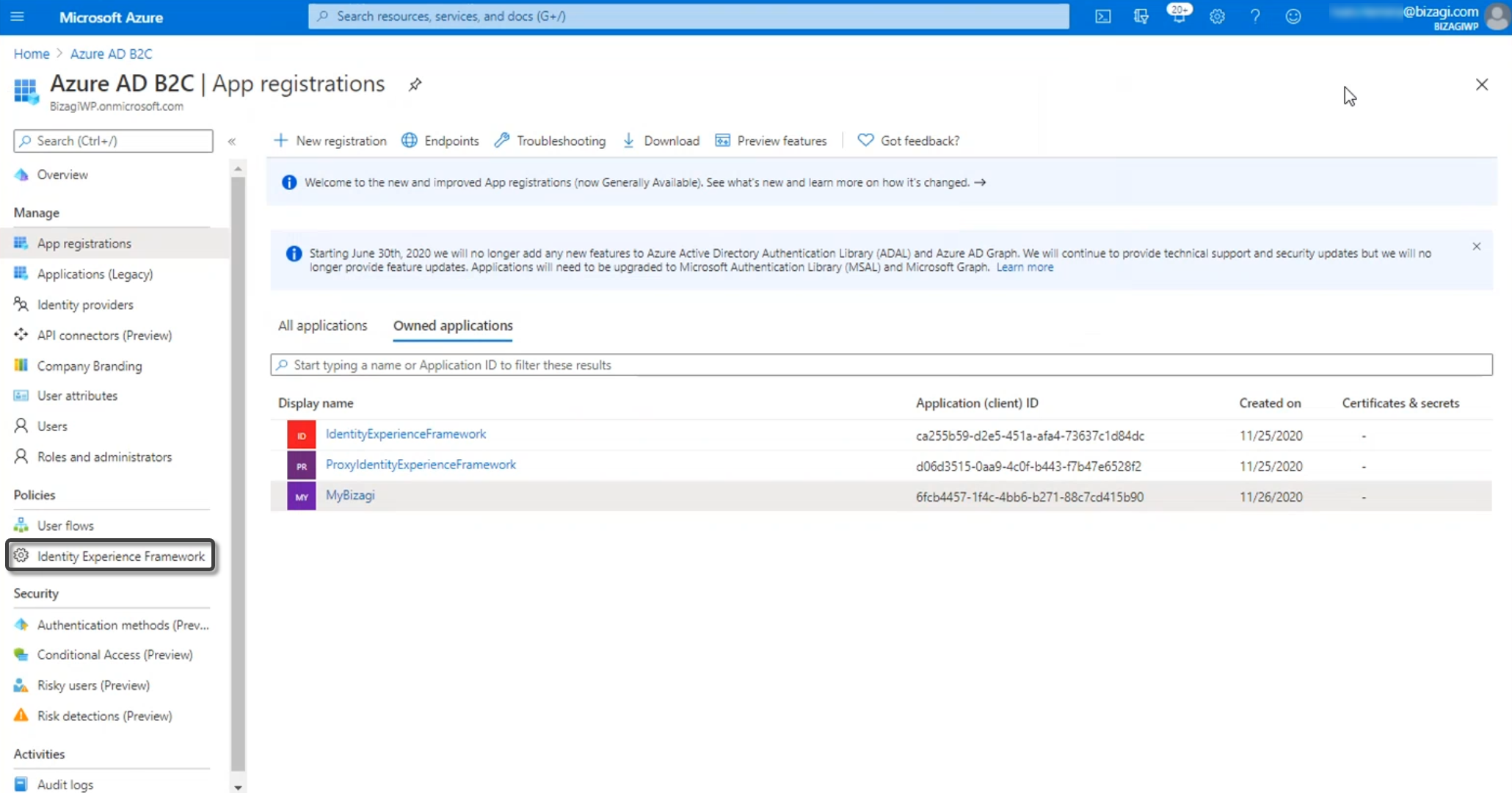
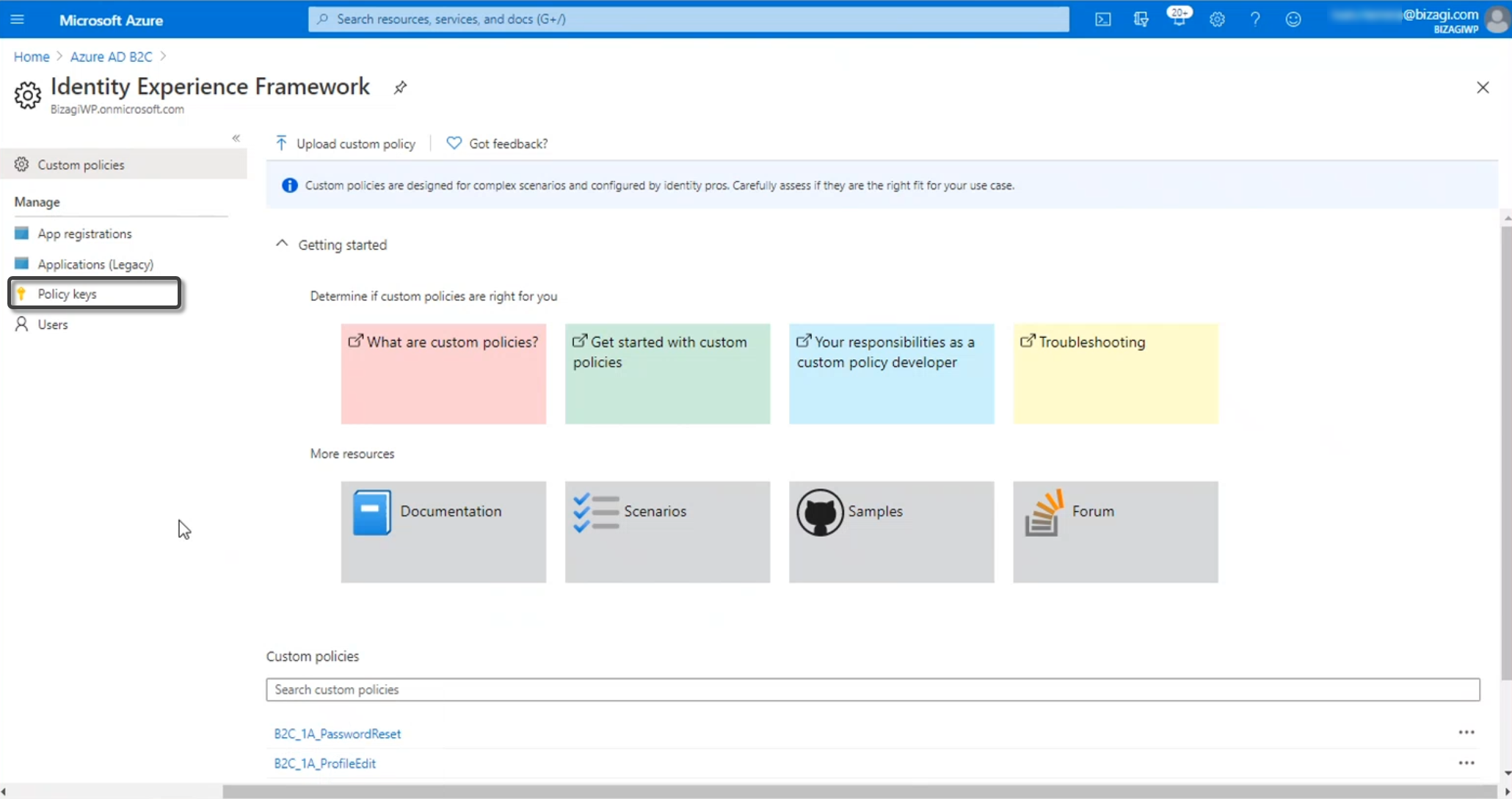
To do so, go to your tenant configuration and go into the Identity Experience Framework.
Note: Bear in mind that you need to be in the subscription and in the active directory where the B2C tenant was created.
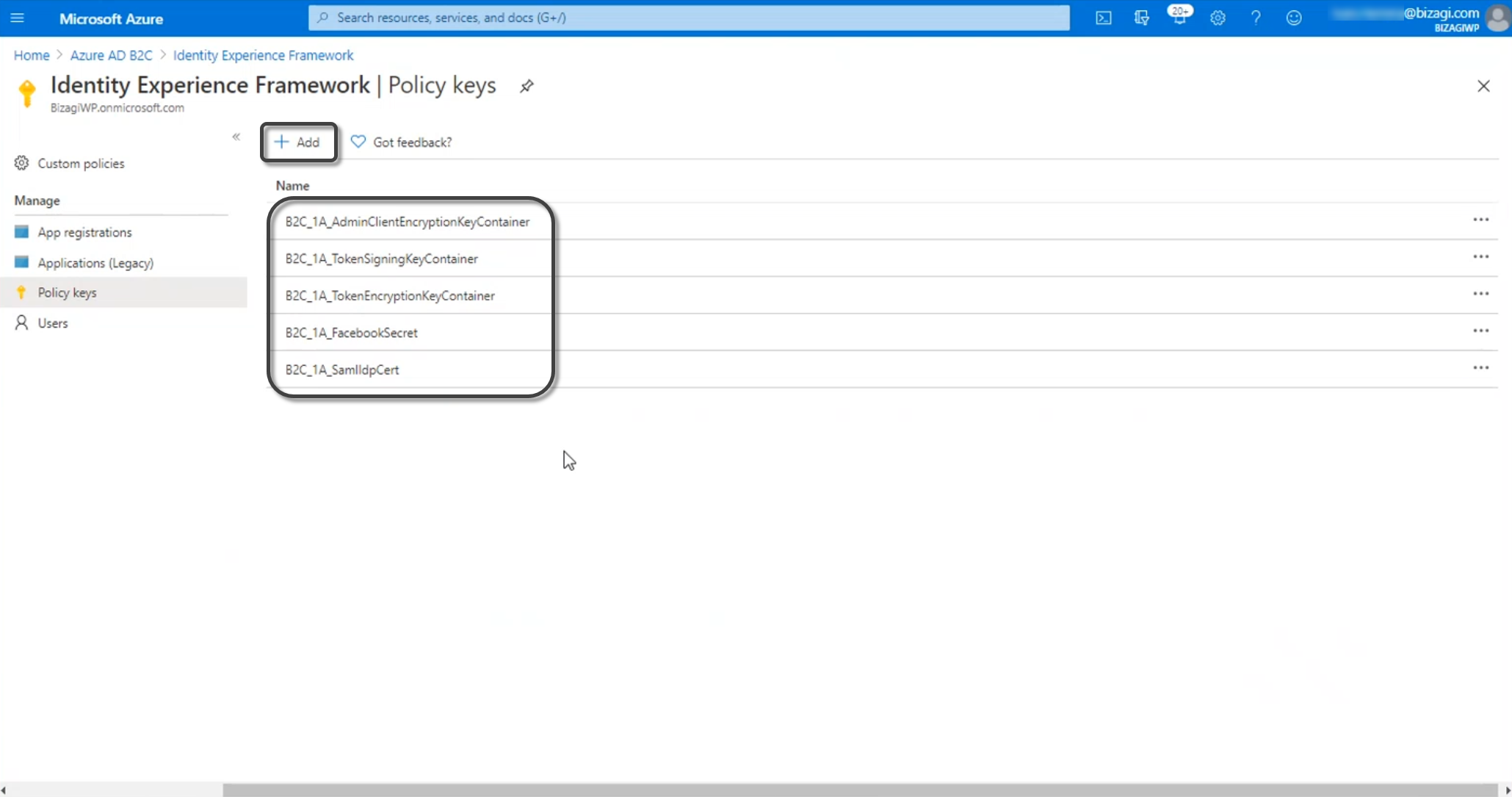
Create the Policy Keys needed to establish trust with the services that you are going to integrate with. For this, click Policy Keys and then click Add.
Register a SAML application in Azure AD B2C.
Now follow these configuration steps.
1. Generate certificates to sign assertions (mandatory)
This step is not bound to Bizagi nor restricted by any special requirement of Bizagi (you normally do it yourself).
If you need some guidance or an example on this step, refer to Certificates for SAML 2.0 authentication.
To proceed with these guided steps, you need to have:
- One certificate to sign assertions (mandatory) in
.P12or.PFXfile format. You need the password for the certificate file, as defined by you when you exported the public and private keys. - One certificate to encrypt messages (optional) in
.P12or.PFXfile format. You need the password for the certificate file, as defined by you when you exported the public and private keys.
Note: You will need to be in charge of managing your installed certificates (keep track of its expiration date and other relevant maintenance aspects such as changes in your Identity Provider's endpoints).
2. Configure your IdP in Bizagi
After you configure the application in Azure AD, now you must access the Bizagi Studio or the Management Console and register the Identity Provider. Follow the steps in Configure a SAML 2.0 IdP in Bizagi.
3. Download the Bizagi metadata file
After you configure the identity provider in Bizagi, you must generate the metadata file. Refer to Download the metadata file.
4. Configure the Azure AD B2C
4.1 Log in to your Azure services with a user account with admin rights.
Access your Azure subscription with the Azure AD service. You will need to sign in to Azure's portal at https://portal.azure.com.
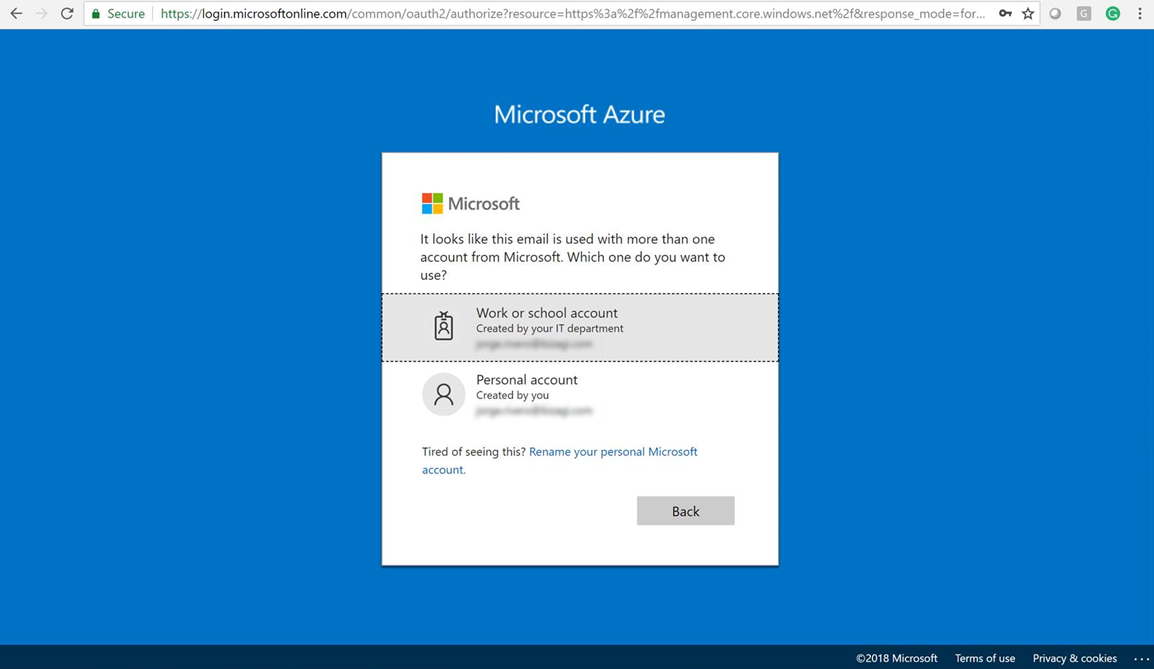
Make sure that you need to be in the subscription and in the active directory where the B2C tenant was created.
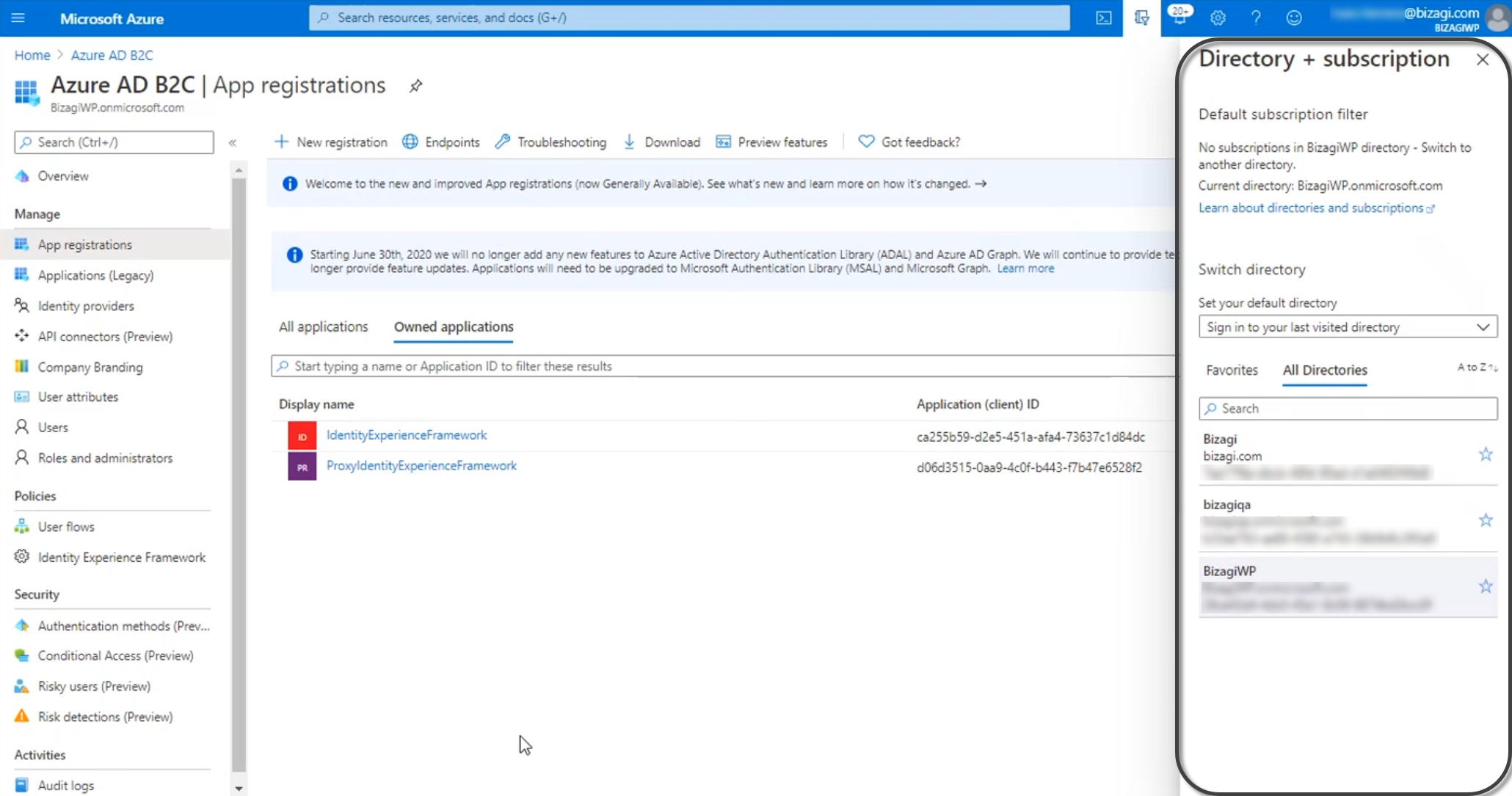
4.2 Register the Application
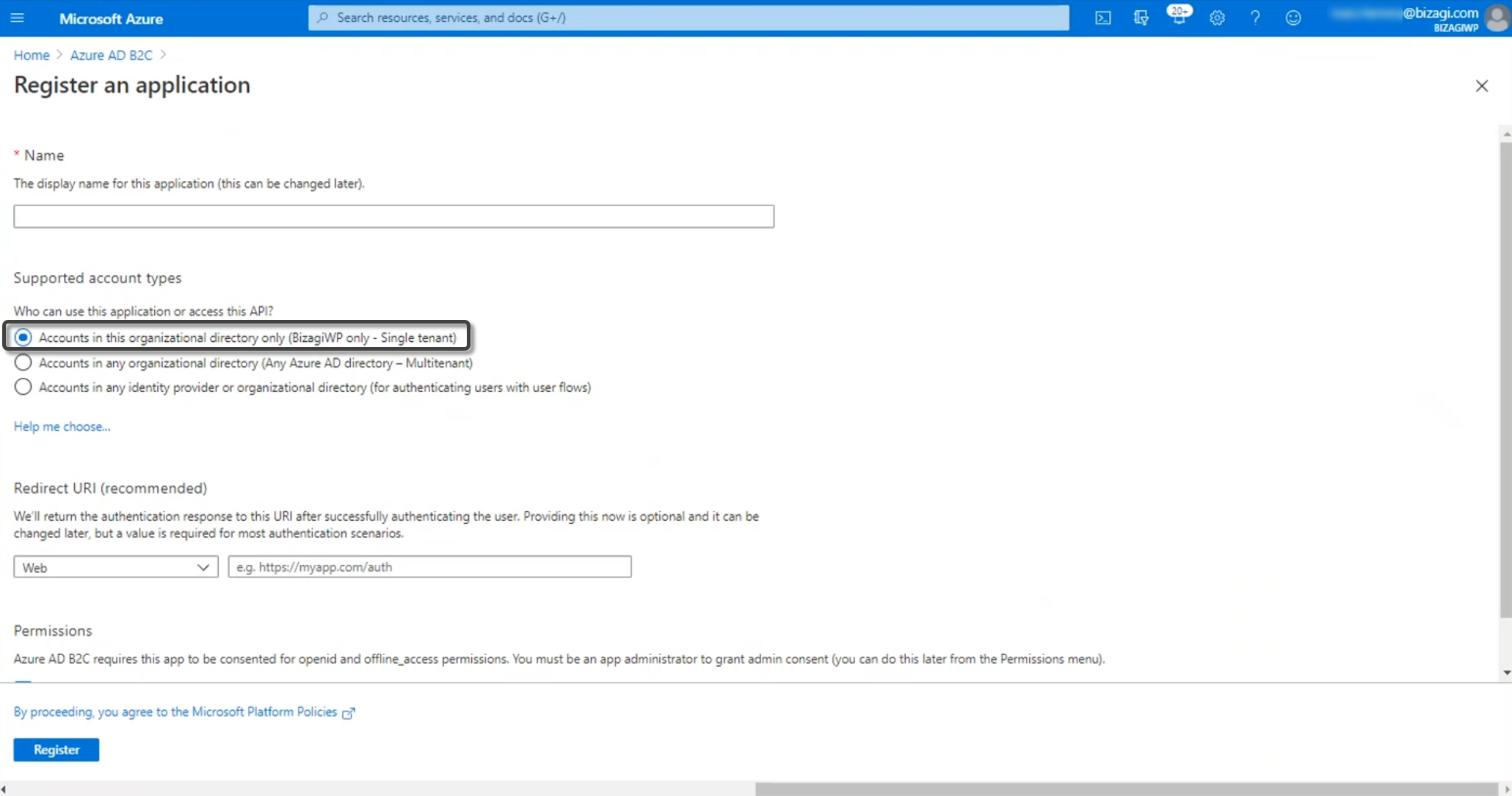
Open the Azure AD, and select the App registrations menu. Click New registration:
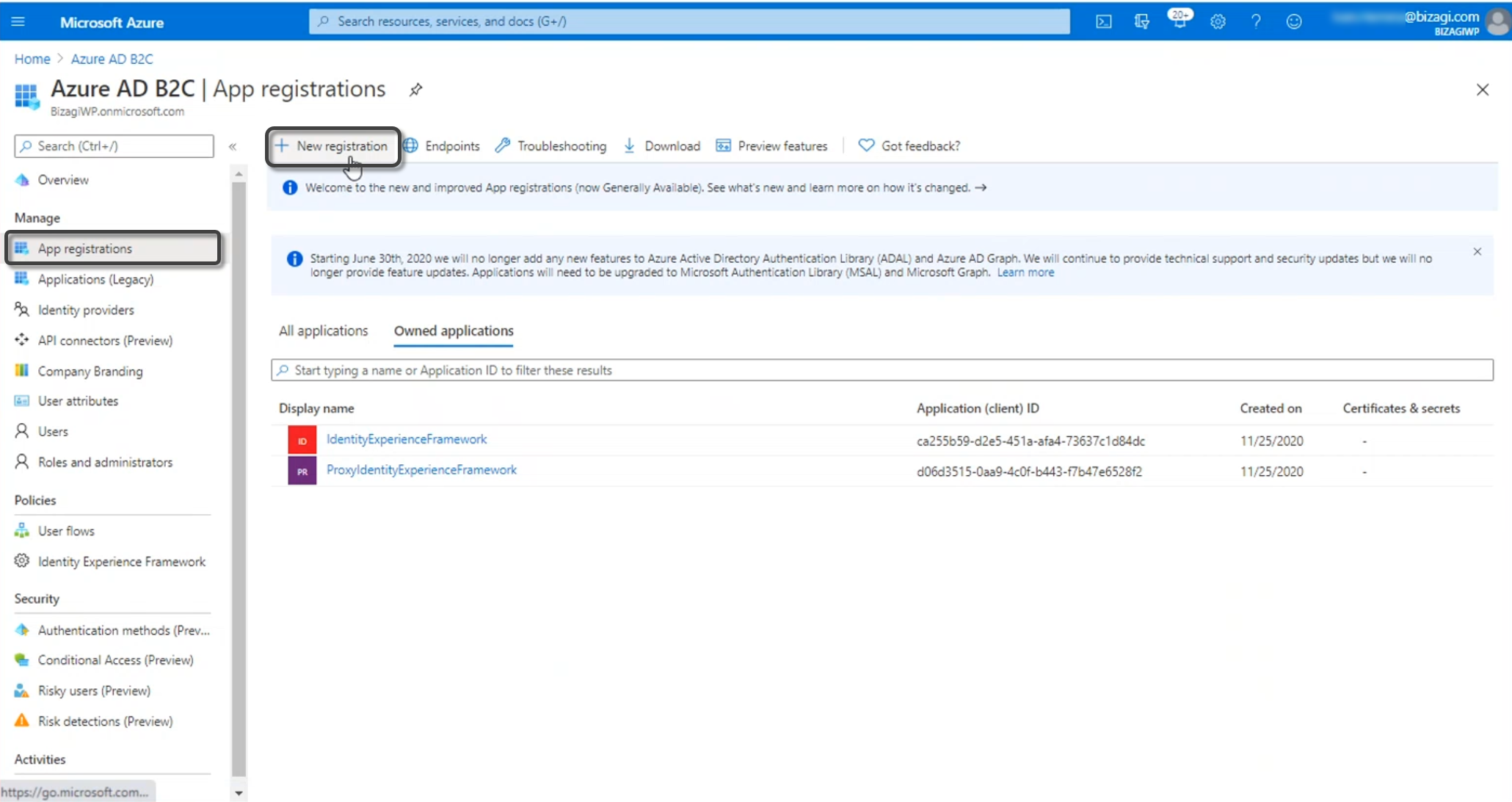
Give a name to your application. Then, select the supported account types. Make sure that you select the tenant associated with the B2C. Finally, type your project's URL.
4.3 Change the application manifest
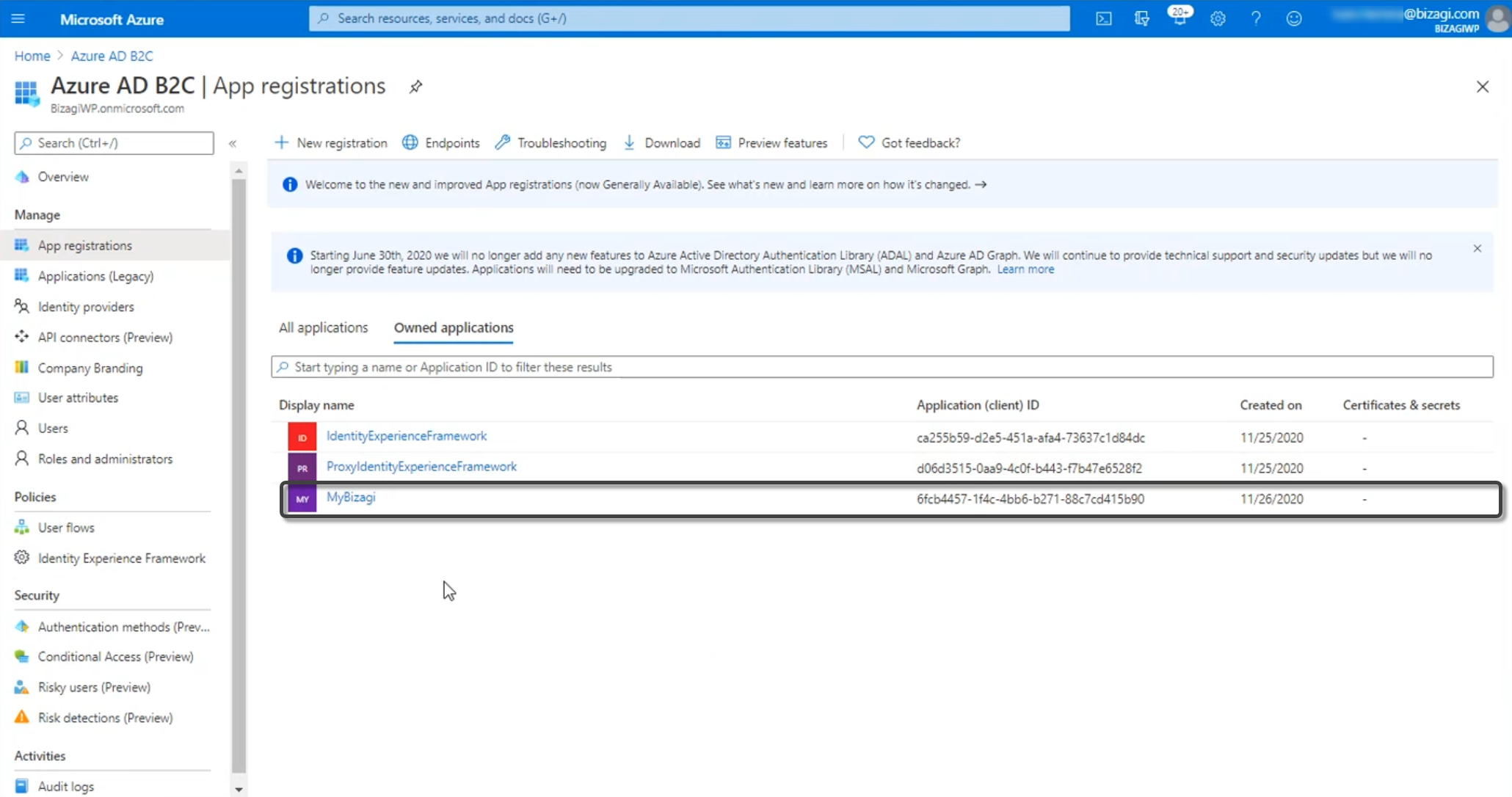
Once your application is registered, you will be able to see it in the App registrations menu. Go to the application.
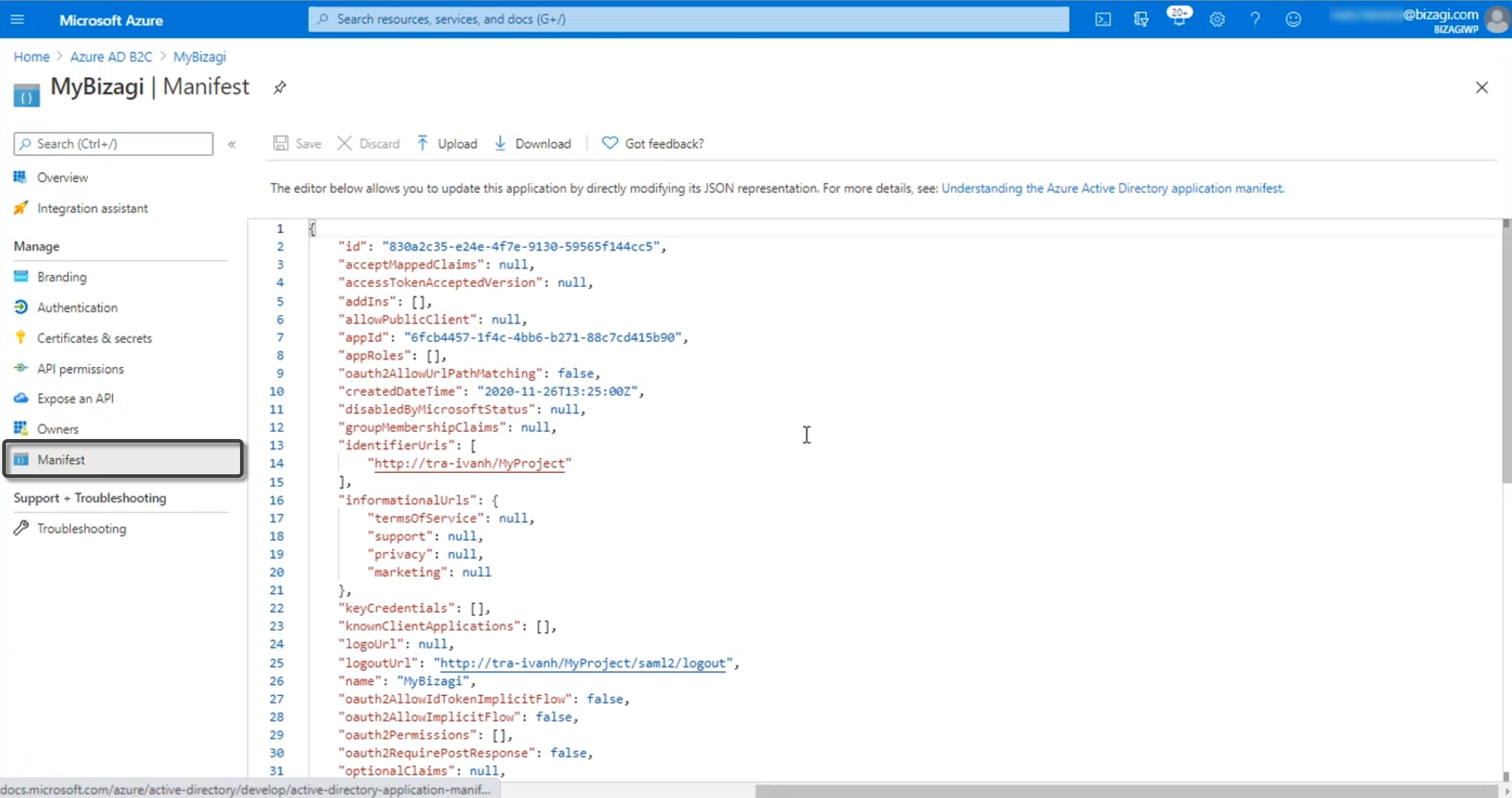
In the manifest, change the following parameters with the values below:
-
identifiersURIs:
https://[environment]-[project]-[company].bizagi.com -
logoutURL:
https://[environment]-[project]-[company].bizagi.com/saml2/logout -
replyURL withType:
url: https://[environment]-[project]-[company].bizagi.com/saml2/assertionConsumer
-
samlMetadataURL:
https://[environment]-[project]-[company].bizagi.com/saml2/metadata?mode=preview -
signInURL:
https://[environment]-[project]-[company].bizagi.com
Additional Keys
You must add the following key: accessTokenAcceptedVersion and set its value to 2:
"accessTokenAcceptedVersion": 2
4.4 Get the metadata URL
Go to the Identity Experience Framework and open the TrustFrameWorkBase file.
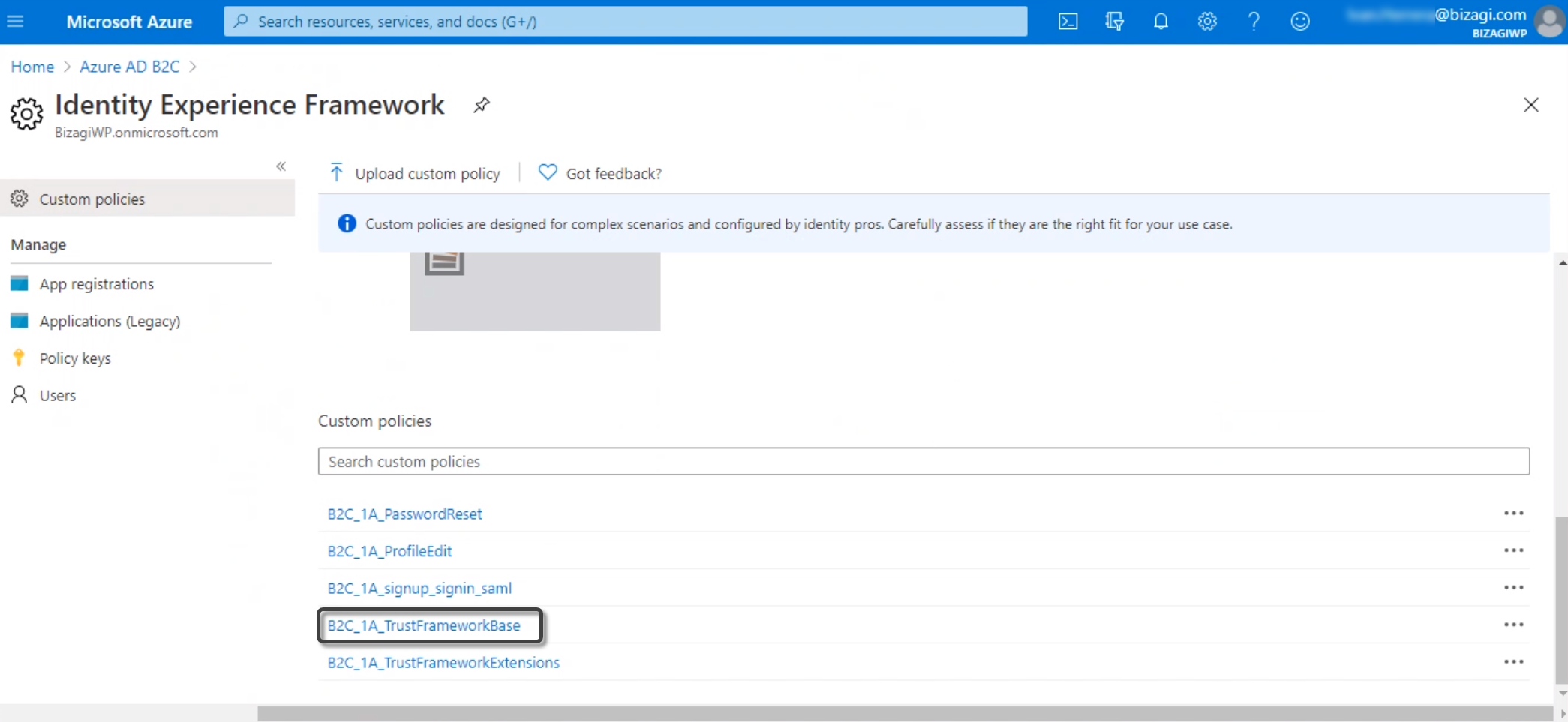
Look for the TechnicalProfile node associated to the SAML protocol. Inside, copy the IssuerUri, which is the metadata URL associated to the SAML assertions generator.
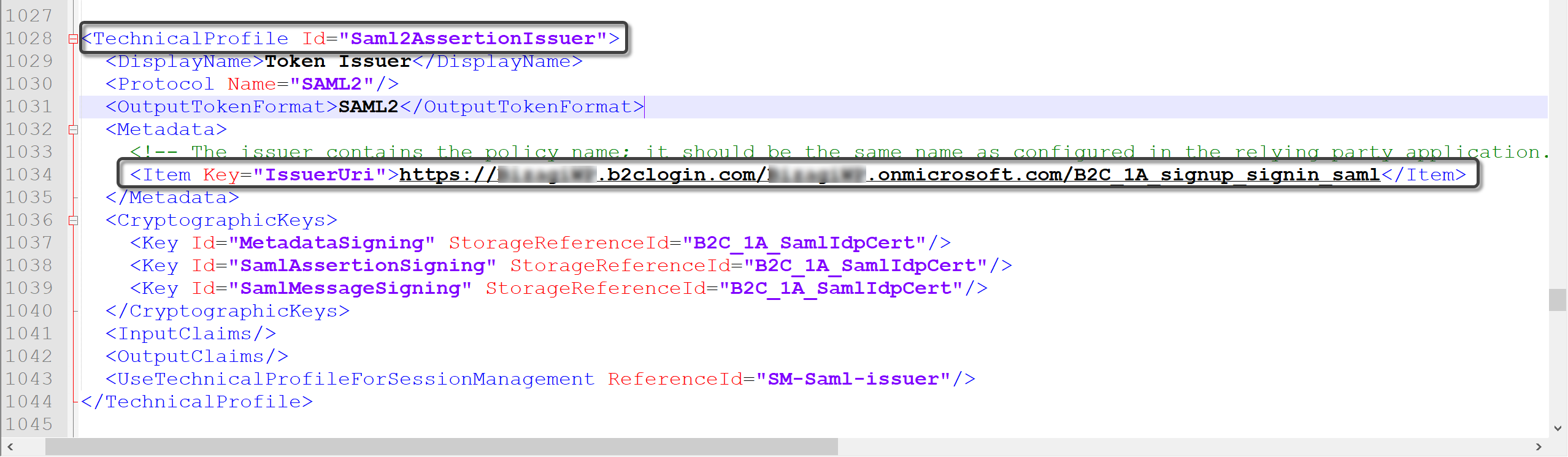
Finally, add the following suffix to the URL copied: Samlp/metadata
Note:
The metadata URL must have the following format:
https://<B2Ctenant>.b2clogin.com/<B2Ctenant>.onmicrosoft.com/B2C_1A_signup_signin_saml/Samlp/metadatawhere
<B2Ctenant>is the name of the B2C tenant created in the Azure AD B2C.
Once you have this file's URL, go back to Bizagi and set it in this key:
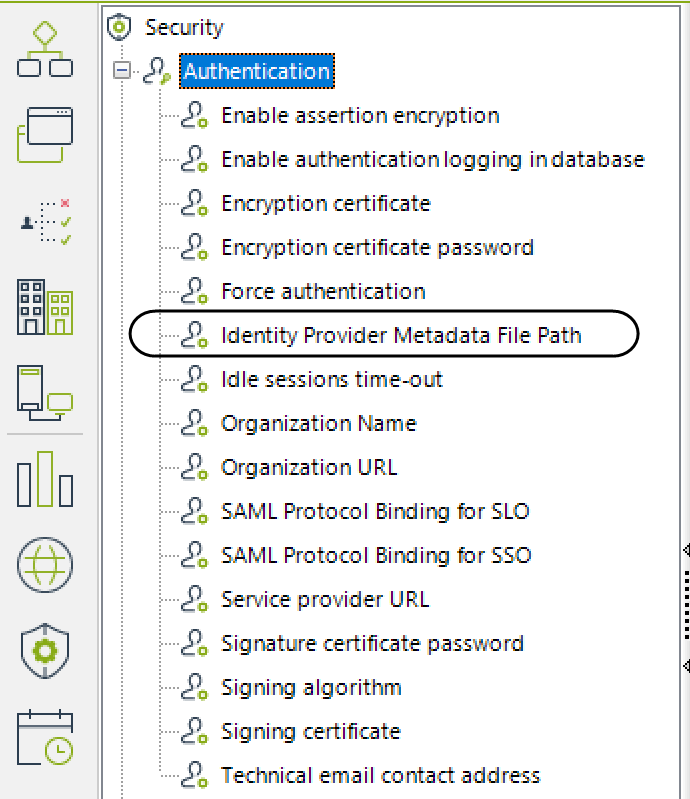
Now when you run the Work Portal, Bizagi displays the IdP's log-in page and users can be authenticated with your IdP.
Note:
Remember to do this configuration in all your environments, or to deploy security configurations in your target environments, for example, test or production environments.